Protect Your Business. Stay Compliant.
End-to-end security and compliance for software teams that cannot afford a breach.
Most businesses discover their security gaps only after an incident. TAK DEVs helps you find and close those gaps before they cost you – with hands-on consulting, rigorous testing, and compliance programmes built around how your team actually works.
- Find vulnerabilities before attackers do
- Meet ISO, GDPR, SOC 2, and HIPAA requirements without delays
- Security built into your pipeline, not bolted on after
- Reduce cloud security risks by up to 35%
- Ship faster with compliance handled end to end


Is Your Business at Risk?
Common threats that grow silently inside software companies.
Cyber threats do not announce themselves. By the time an organisation detects a breach, the damage – financial, legal, and reputational – is already done.
- A data breach costs an average of $4.45 million globally (IBM, 2023)
- Regulators can fine businesses up to 4% of annual global turnover under GDPR
- 73% of small-to-mid-size businesses lack a formal incident response plan
- Supply chain and third-party vendor risks are the fastest-growing attack surface
If your team ships software but does not have a structured security and compliance programme, you are carrying risk that compounds every sprint.
End-to-End Security Coverage
Six disciplines. One integrated security programme.
Security Consulting & Risk Assessment
Find the gaps before attackers do.
Our security consultants assess your systems, infrastructure, and processes against real-world attack vectors.
- Threat modelling across your entire technology stack
- Gap analysis against NIST, ISO 27001, and CIS benchmarks
- Prioritised remediation roadmap with effort and impact scoring
- Board-ready reporting to support procurement and investor due diligence
Ideal for organisations preparing for a compliance audit, a funding round, or a major product launch.
Application Security Testing
Secure the code before it ships.
Application vulnerabilities are the primary entry point for modern attacks. Our testing finds them before your users – or attackers – do.
- OWASP Top 10 vulnerability assessment
- Static and dynamic analysis (SAST / DAST)
- API security testing including authentication and rate-limiting gaps
- Manual penetration testing by certified security engineers
- Remediation support so findings get fixed, not just filed
Required for SOC 2 Type II, PCI DSS, and HIPAA-compliant software products.
Data Protection & Encryption
Keep sensitive data safe at every layer.
Data is the most valuable – and most targeted – asset your business holds. We design and implement protection that holds up under audit and under attack.
- Data classification and inventory mapping
- Encryption strategy for data at rest and in transit
- Key management and secrets rotation
- Data retention and deletion policies aligned to GDPR and CCPA
Privacy by design embedded into your development workflow
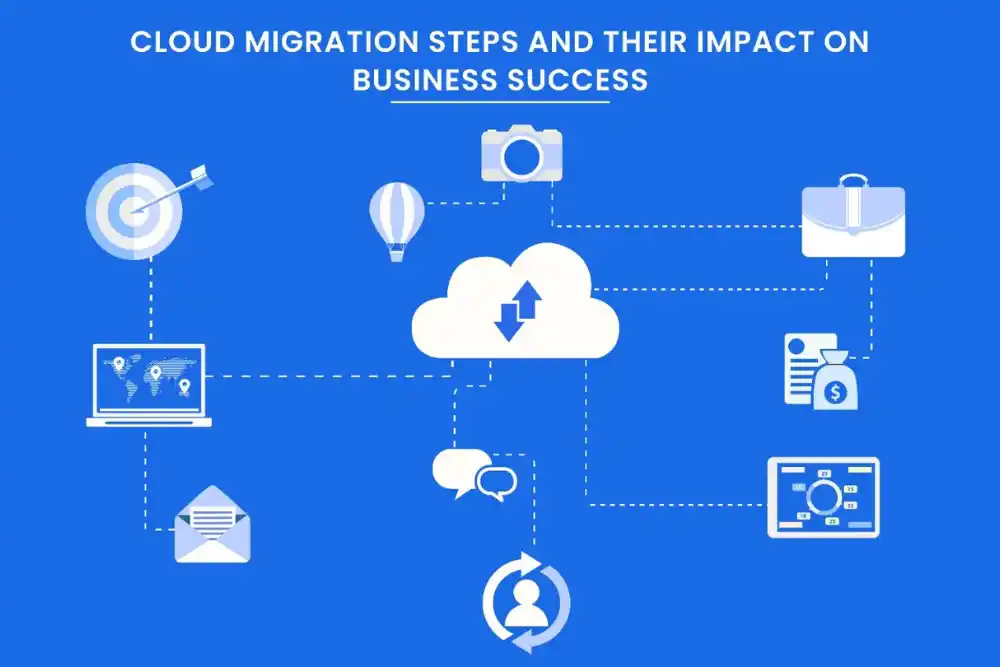
Cloud Security
Protect AWS, Azure, and GCP environments.
Misconfigured cloud environments are responsible for a large share of enterprise breaches. We harden your cloud posture and keep it there.
- Cloud security posture management (CSPM) across major cloud providers
- Identity and access management (IAM) review and least-privilege enforcement
- Infrastructure-as-code (IaC) security scanning
- Runtime threat detection and alerting
- Cost and compliance optimisation – typical savings of 20-35% on cloud spend
Compliance - ISO, GDPR, SOC 2 & More
Meet standards without stalling your roadmap.
Compliance is not a checkbox exercise. Done well, it becomes a competitive advantage – proof to customers, partners, and regulators that you take data seriously.
- ISO 27001 – gap assessment, controls implementation, and audit preparation
- GDPR and UK GDPR – DPA, DPIA, and lawful basis review
- SOC 2 Type I and II – readiness assessments and evidence support
- HIPAA – required safeguards for health data and covered entities
- PCI DSS – cardholder data environment scoping and controls
Cyber Essentials and Cyber Essentials Plus – UK government-backed certification
DevSecOps Integration
Security baked into every deployment.
Security added at the end of a sprint is expensive to fix and disruptive to ship. We integrate security into your pipeline so it moves with your team, not against it.
- Security-as-code policies in your CI/CD pipeline
- Automated vulnerability scanning on every pull request
- Secrets detection and prevention before code reaches production
- Container and dependency security monitoring
- Developer security training tailored to your stack
Supports SOC 2, ISO 27001, and PCI DSS continuous compliance requirements.
Trusted and recognized across the industry

How TAK Devs Works
Process diagrams look the same at every agency. What matters is what actually happens inside each phase. Here is how we work in practice:
Discovery Call
A focused conversation to understand your goals, challenges, and vision. We ask the right questions to uncover what you truly need — before a single line of code is written.
Scoping Workshop
We translate your goals into a clear, actionable plan. Features are prioritised, timelines are set, and everyone aligns on what success looks like eliminating guesswork from day one.
Sprint Delivery
We build in short, focused cycles, shipping real, working software every sprint. You see progress continuously, give feedback early, and stay in control of where the product is heading.
Launch & Handoff
Your product goes live with confidence. We handle deployment, documentation, and knowledge transfer, ensuring your team is fully equipped to own and operate what we built together.
Ongoing Support
Our relationship doesn't end at launch. We monitor, maintain, and improve your product over time, fixing issues fast and helping you evolve as your users and business grow.
Struggling to keep up with development demands?
See how we can streamline your workflow.
No commitment required | Takes 20 minutes !

Industries We Have Built For
We list these not to claim expertise across everything, but to be specific about where we have direct experience. Domain knowledge matters because understanding the compliance constraints of healthcare or the latency requirements of financial systems shapes architecture decisions that general experience misses.

Legal Technology
- Case workflow automation
- Secure document management
- AI legal research
- Compliance tracking systems

Health Tech
- Patient data management
- Telehealth platform integration
- Electronic health records
- Healthcare analytics tools

AUTOMOTIVE & MOBILITY
- Fleet management systems
- Connected vehicle solutions
- Mobility app development
- Predictive maintenance tools

Retail & E-commerce
- Omnichannel shopping experience
- Inventory management systems
- Conversion rate optimization
- Personalized product recommendations

Consulting Providers
- Data-driven decision making
- Business process automation
- Client collaboration tools
- Performance tracking dashboards

Travel & Hospitality
- Online booking systems
- Guest experience optimization
- Property management software
- Dynamic pricing solutions
Who TAK Devs Works With

Founders and Early-Stage Startups
If you are shipping a product that handles user data and you do not yet have a formal security programme, you are one breach away from losing customer trust - and potentially your licence to operate.

CTOs and VP Engineering
You have inherited a codebase or cloud environment with unknown risk. The security debt is growing and no one has mapped it. Modernising legacy systems with compliance requirements Need DevSecOps implemented without slowing sprint velocity Managing a growing team where secure coding practices are inconsistent

Operations and Data Leaders
You are accountable for regulatory compliance but lack dedicated security engineering resource in-house. Preparing for an external audit or regulatory review Need a compliant data handling programme documented and evidenced Managing vendor risk and third-party security assessments
What Working With TAK Devs Actually Looks Like
In early 2025, UpliftCare came to us with a clear challenge and a tight window. They needed a complete, HIPAA-compliant telehealth marketplace connecting patients, verified therapists, and healthcare institutions. The deadline was three months, set by an investor presentation they could not move.
There was no technical architecture. No defined roadmap. Just a vision and a date.

TAK Devs took on the full product lifecycle.
In six sprints and twelve weeks, we delivered:
Four connected portals covering Patient, Therapist, Admin, and Institutional workflows
Real-time video consultations via WebRTC, integrated Stripe payments, and smart scheduling
100% HIPAA-aligned architecture with full encryption across all data flows
Automated credential verification that reduced therapist onboarding time by 70%
CI/CD pipelines, automated testing, and AWS-based deployment ready for production from day one
Security and engineering under one roof.
Engineering-native security
Our consultants have shipped production software
No dependency on compliance theatre
We tell you what is actually broken, not just what an auditor wants to see
Fixed-price options available
No open-ended retainers that grow without scope
Honest fit assessment
If we are not the right partner, we will say so on the first call
Testimonials










Frequently Asked Questions
What is included in a cybersecurity compliance service?
Cybersecurity compliance services help organisations identify security risks, implement controls, and meet regulatory standards such as ISO 27001, GDPR, SOC 2, and HIPAA. At TAK DEVs, our service covers:
- Security risk assessments and gap analysis
- Technical testing (penetration testing, application security, cloud configuration review)
- Policy and procedure documentation
- Compliance programme management and audit preparation
- Ongoing monitoring and incident response planning
How long does ISO 27001 certification take?
For most small-to-mid-size organisations, the journey from gap assessment to certification takes between 3 and 12 months, depending on your current security maturity and the scope of your Information Security Management System (ISMS). TAK DEVs can accelerate this by:
- Starting with a rapid gap assessment to identify the shortest path to certification
- Using pre-built, auditor-approved policy templates adapted to your business
- Running implementation in parallel with your product roadmap, not blocking it
Do you work with early-stage startups?
Yes. Many of our clients are seed-to-Series B companies that need to pass enterprise security questionnaires or achieve compliance certification as part of a funding or partnership requirement. We offer scoped engagements that fit startup budgets and timelines.
What is the difference between a security audit and a penetration test?
A security audit reviews your policies, controls, and processes against a standard (such as ISO 27001 or NIST) and identifies gaps in documentation and governance.
A penetration test simulates an attacker actively trying to break into your systems – finding exploitable vulnerabilities that automated scanners and audits miss.
Most compliance frameworks require both. TAK DEVs delivers both, so findings align and remediation is coordinated.
Can you integrate security into our existing development pipeline?
Yes – this is one of our core specialisms. Our DevSecOps service embeds security tooling and practices directly into your CI/CD pipeline, including:
- Automated SAST and DAST scanning on every pull request
- Secrets detection before code reaches production
- Container image scanning and software composition analysis (SCA)
- Security gates that flag critical issues without blocking standard deployments
We work with GitHub Actions, GitLab CI, CircleCI, Jenkins, and other major pipeline tools.
How much does cybersecurity compliance cost?
Cost depends on the scope of services, your organisation size, and the compliance framework involved. We offer:
- Fixed-price assessments – starting with a defined-scope security review
- Project-based compliance programmes – with transparent milestone pricing
- Retained security support – for ongoing monitoring and compliance maintenance
The most accurate way to get a number is a 20-minute discovery call. We scope honestly and do not inflate estimates.
We already have a CTO. Do we still need security consultants?
CTOs manage product delivery, team performance, and technical strategy – security compliance is a specialist discipline on top of that. Most CTOs benefit from a dedicated security partner who:
- Owns compliance programmes end-to-end, freeing engineering leadership to ship
- Brings cross-industry experience that internal teams rarely accumulate
- Provides independent assurance that regulators and auditors require
Our vCISO-style engagements are designed specifically to complement existing technical leadership, not replace it.
What happens after a security assessment?
Every TAK DEVs assessment delivers a prioritised remediation report with:
- Critical, high, medium, and low severity findings
- Business impact explanation for each finding
- Specific, actionable remediation steps – not generic recommendations
- Effort estimates to help your team plan and resource fixes
We then offer remediation support to work alongside your engineers on the most complex fixes, ensuring findings are resolved correctly – not just closed on a spreadsheet.
Is our data safe during a security engagement?
Yes. TAK DEVs operates under strict data handling agreements for all engagements. We:
- Sign NDA and data processing agreements before any work begins
- Limit data access to the minimum required for testing and assessment
- Securely delete client data at the end of each engagement
- Operate under our own ISO-aligned information security policies